AI News
20 Nov 2025
Read 14 min
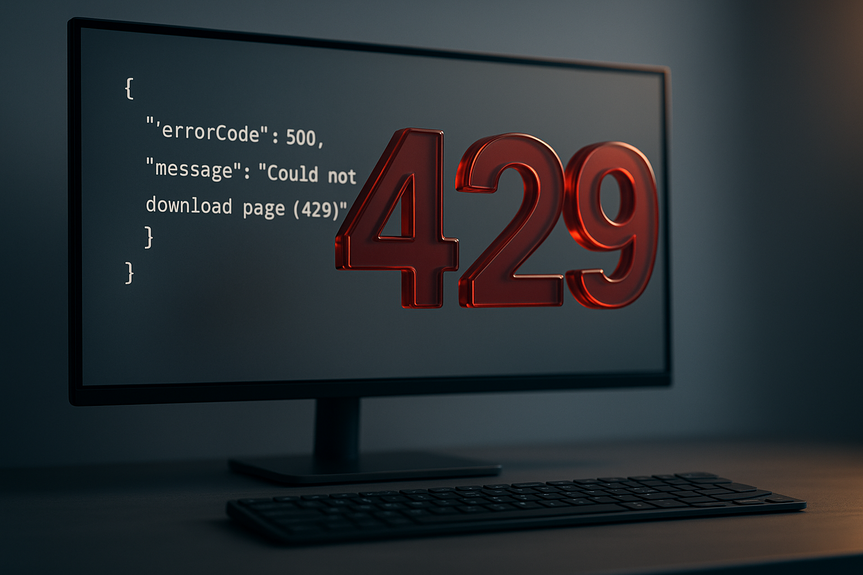
Fix HTTP 429 error now with 7 proven fixes
Fix HTTP 429 error quickly to restore uninterrupted access and stop rate limiting from blocking users.
What HTTP 429 means and why you see it
The 429 status is “Too Many Requests.” A rate limiter stands between you and the target. It can sit in an API gateway, a CDN like Cloudflare, a web server like Nginx, or in the app code. When your traffic is too fast or too bursty, the limiter blocks new requests for a while. Look for these headers when 429 hits:- Retry-After: tells you how long to wait (seconds or a date/time).
- X-RateLimit-Limit: the allowed number of requests in a time window.
- X-RateLimit-Remaining: how many requests you have left right now.
- X-RateLimit-Reset: when the window resets.
- Bursts from parallel requests (for example, 50 tabs or 100 async calls at once).
- Polling too often instead of using webhooks or longer intervals.
- Authentication loops that retry on 401/403 and snowball into 429.
- Scripts or bots crawling with no delay or ignoring robots rules.
- Server rules that are too strict for real user traffic.
How to fix HTTP 429 error: 7 proven fixes
1) Respect Retry-After and use exponential backoff
The fastest way to recover is to wait as the server asks.- Read the Retry-After header. If it says “30,” wait 30 seconds before retrying.
- If the header is missing, start with a short delay and back off: 1s, 2s, 4s, 8s… up to a safe cap.
- Stop retrying after a few attempts (for example, 5) to avoid hammering the server.
- Add jitter (a small random extra delay) so many clients do not retry at the same second.
2) Throttle and batch your requests
Limit how many calls you send at once. Spread them out.- Set a global rate: for example, 5 requests per second max for one token or IP.
- Limit concurrency: cap to N parallel calls at a time (example: 3).
- Queue extra work: line up calls and release them at a steady pace.
- Batch small operations: combine multiple items into one request if the API allows it.
3) Cache, reuse, and dedupe
Many 429s come from repeated, identical requests.- Cache static and semi-static responses (minutes or hours, based on data needs).
- Use strong validators: ETag and If-None-Match to avoid full responses if nothing changed.
- Deduplicate in-flight requests: if two parts of your app ask for the same data, let the second wait for the first result.
- Share a cache across workers or instances so they do not re-fetch the same data.
4) Make each request carry more value
Reduce the number of calls by asking for what you need, the right way.- Use pagination with larger but safe page sizes (for example, 100–500 items instead of 10).
- Filter and select fields so the server returns only what you use.
- Use bulk endpoints when they exist (create or update many items at once).
- Replace tight polling with webhooks, server-sent events, or longer polling intervals.
5) Fix auth loops and bot behavior
429 can hide behind other bugs.- Check your tokens: avoid retry loops that keep sending invalid or expired keys.
- Refresh tokens early (for example, when 10% of time-to-live remains).
- Set sane retry rules: do not retry on 401/403 without a change (like a fresh token).
- If you run a crawler or scraper, obey robots.txt, set a clear User-Agent, add delays, and crawl during off-peak hours.
6) Tune server, CDN, and WAF rate limits
If you control the server or edge, adjust the rules so real users are not blocked.- Use sliding-window or token-bucket rate limiting instead of simple fixed windows to avoid sharp cutoffs.
- Set separate limits by route, user, token, or IP. Heavy endpoints may need stricter caps.
- Add a burst allowance so short spikes pass but sustained floods do not.
- Whitelist trusted internal services and health checks.
- In CDNs or WAFs, tune bot protection so it does not hit normal browsers.
7) Raise your quota or change your plan
Sometimes your app has grown and you hit the ceiling.- Ask the provider for a higher rate limit or a paid plan with more headroom.
- Spread heavy jobs over time (nightly windows) or across regions if allowed.
- If legal and allowed, use separate credentials for separate users so each has a fair slice.
- Avoid shady proxy farms. They may break terms of service and get you banned.
Diagnose the root cause before you change things
Go step by step so you fix the right thing the first time.- Reproduce: hit the same endpoint with the same payload and watch headers and timing.
- Check rate-limit headers: confirm your current allowance, remaining tokens, and reset time.
- Graph requests per minute by route, user, and IP. Find bursts or loops.
- Review deploys and cron jobs around the time 429s started.
- Ask support for your account’s limits and recent blocks if the provider is external.
Client-side patterns that keep you safe
Keep traffic smooth even when users click fast.- Debounce and throttle UI actions: limit how often buttons can fire network calls.
- Merge duplicate reads from fast-moving components into one call.
- Preload and prefetch wisely: not on every hover, only when needed.
- Use offline queues and sync intervals on mobile so you do not burst on reconnect.
Server-side patterns that scale
On your own API, prevent abuse and keep honest users happy.- Rate limit per API key or session instead of only by IP (shared IPs can punish good users).
- Protect costly endpoints (search, exports) with stricter rules and background jobs.
- Provide bulk endpoints and webhooks so clients do not need to poll.
- Return helpful headers (Retry-After and X-RateLimit-*) so clients can adapt.
- Queue long tasks and stream progress instead of forcing many short polls.
Monitoring and alerts for peace of mind
You cannot manage what you do not measure. Set up:- Dashboards for 2xx/4xx/5xx rates, with a dedicated chart for 429 over time.
- Alerts when 429 crosses a threshold, per service and per customer tier.
- Logs that attach user ID, IP, route, and correlation IDs to each 429.
- Tracing that shows where retries and delays are added in your code path.
Real-world examples of what works
- E-commerce: Users spam the “Add to cart” button. Solution: UI debouncing and server limit of 3 cart writes per second per session. Result: 429 drops to near zero.
- Data sync: Mobile app reconnects and fires 500 requests. Solution: queue on device, 5-per-second throttle, and backoff on 429. Result: faster sync, no bans.
- Analytics API: Nightly job pulls 1M rows with tiny pages. Solution: larger pages, ETags, and bulk export endpoint. Result: 90% fewer requests.
- SaaS API client: Token expires and code retries forever. Solution: refresh tokens early and stop retries after 3 tries. Result: stable traffic and fewer errors.
A short checklist you can run today
- Add exponential backoff with jitter on all non-idempotent retries.
- Throttle to a safe per-second rate and cap concurrency.
- Cache common responses and dedupe in-flight calls.
- Increase page size and reduce polling where possible.
- Fix authentication refresh and stop retry loops.
- Tune rate limits on your edge and API routes.
- Contact the provider to raise limits if your business needs it.
(Source: https://cw39.com/news/education/hisd-announces-ai-tools-for-teachers-using-chat-gpt/)
For more news: Click Here
FAQ
Contents