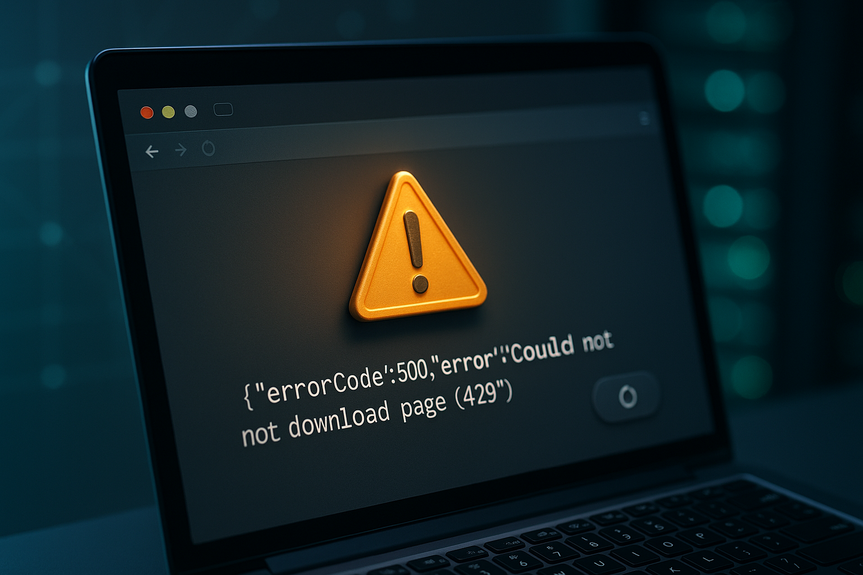
How to fix 429 Too Many Requests error and restore site access fast with server and rate limit fixes
Learn how to fix 429 Too Many Requests error fast. This status means the server is blocking you because it got too many hits in a short time. Wait and retry after the time shown in the Retry-After header, reduce parallel calls, close extra tabs, and use backoff logic in your app to stay under limits.
A 429 happens when you or your app send requests faster than a site or API allows. The block can be based on your IP, account, or API key. Good news: you can lower the request rate, pause for a bit, and try again. If you build software, add smart retry rules. If you run a site, tune rate limits and caching.
How to fix 429 Too Many Requests error: quick wins
If you are browsing
Stop clicking refresh. Wait at least 30–60 seconds. If the response shows a Retry-After header, wait that many seconds.
Close duplicate tabs, paused downloads, and auto-refresh tools that may hammer the site.
Turn off aggressive browser extensions (ad blockers, scrapers, auto-checkers). Then reload.
Sign in if the site supports accounts. Logged-in traffic may have a higher limit.
Clear cache and cookies, then try again. Or open a private window.
Disable VPN or proxy for a moment. Some providers rate-limit shared IPs.
Switch networks (mobile hotspot vs. Wi‑Fi) to test if your IP is blocked.
If you are using a public API
Read the response headers. Look for Retry-After, X-RateLimit-Limit, X-RateLimit-Remaining, and reset times.
Pause requests until the reset time. Then resume at a lower rate.
Check your account dashboard for quota use and bursts.
Upgrade your plan or request higher limits if you regularly hit the cap.
Find the root cause before you retry
Common triggers
Loops or retries without delay in your code.
Too many concurrent requests (threads, workers, tabs).
Polling too often (every second) instead of using webhooks or events.
Multiple services calling the same API with the same key.
Automated crawlers that ignore robots.txt or crawl-delay.
How to spot them fast
Open your network panel (browser dev tools) and watch request counts per second.
Check server or app logs for spikes. Note user, key, IP, and endpoint.
Locate hot endpoints (login, search, auth/token) that often cause 429s.
Compare time windows with provider limits. Align your schedule with their reset time.
Developer fixes that work now
Respect limits and wait smartly
Always honor Retry-After. If none, use exponential backoff with jitter: wait 1s, 2s, 4s, 8s, plus a small random delay.
Cap retries to avoid storms. Log and surface a clear message to users.
Reduce request volume
Cache responses with proper TTL. Avoid calling the same endpoint for every page load.
Batch and paginate. Request 100 items once instead of 1 item 100 times.
Collapse duplicate calls (request coalescing) within a short window.
Prefer webhooks or server-sent events over tight polling.
De-duplicate retries across workers with a queue (Redis, SQS, RabbitMQ).
Control concurrency
Set a global request budget per user or key. Example: no more than 5 in-flight API calls.
Use a token bucket or semaphore to throttle parallel work.
Stagger jobs and cron tasks. Spread traffic over each minute, not on the minute.
Be a good client
Send a clear User-Agent and contact header. Many providers block unknown scrapers.
Use conditional requests (ETag/If-None-Match) to save calls.
Handle other errors (401/403/5xx) differently. Do not retry them like 429.
This guide shows how to fix 429 Too Many Requests error in minutes by slowing down, batching, and honoring server hints.
Site owner and API provider playbook
Set fair limits
Rate-limit by account or API key first. Fall back to IP for anonymous users.
Use sliding windows or token buckets to allow short bursts but protect the system.
Return Retry-After with 429 to guide clients.
Harden hot paths
Cache heavy reads at CDN or reverse proxy (Cloudflare, Fastly, Nginx). Add cache keys with auth where safe.
Protect login and auth/token endpoints with stricter limits and bot checks.
Add request collapsing for identical upstream fetches.
Tune infrastructure
Nginx: use limit_req with a burst and proper status=429; serve a small JSON with Retry-After.
Apache: mod_ratelimit or mod_evasive to slow or block bursts.
WAF/CDN: enable managed rules, bot fight modes, and per-path policies.
During maintenance, send 503 with Retry-After instead of letting 429s spike.
Watch and adjust
Log rate-limit events with key, IP, path, and reason. Build alerts on spikes.
Publish your limits and examples in docs. Show remaining quota headers.
Give developers a test sandbox with lower limits and clear resets.
Prevent it from coming back
Simple habits
Space out background jobs. Randomize start times.
Keep a small safety margin under provider limits (for example, target 80% of max).
Add dashboards for requests/sec, error rates, and retry counts.
Run load tests before a big launch. Validate backoff and queuing logic.
Educate your team so each service does not retry at once.
You now know how to fix 429 Too Many Requests error with fast steps and solid long-term practices. Pause and honor Retry-After, cut duplicate calls, and throttle concurrency. If you run a site, expose clear limits and cache heavy paths. These moves restore service quickly and keep it stable.
(Source: https://www.kron4.com/news/technology-ai/cal-state-students-widely-use-ai-tools-but-mistrust-results-fear-job-impact-survey/)
For more news: Click Here
FAQ
Q: What does a 429 Too Many Requests error mean?
A: A 429 Too Many Requests error means the server is blocking you because it received too many requests in a short time. If you want to know how to fix 429 Too Many Requests error, start by honoring the Retry-After header, waiting 30–60 seconds if no header, and reducing parallel requests or duplicate tabs before retrying.
Q: What immediate steps should I take if I see a 429 in my browser?
A: Stop clicking refresh and wait at least 30–60 seconds or the number of seconds shown in the Retry-After header if present. Close duplicate tabs and paused downloads, turn off aggressive browser extensions, sign in if the site supports accounts, clear cache or use a private window, or briefly disable VPN or switch networks to test if your IP is rate-limited.
Q: How should developers modify their apps to prevent 429 errors?
A: Developers should honor Retry-After headers and implement exponential backoff with jitter, capping retries to avoid retry storms. They should also reduce request volume by caching, batching or paginating, collapsing duplicate calls, using webhooks instead of tight polling, and controlling concurrency with a token bucket or a small in-flight limit (for example no more than five concurrent API calls).
Q: How can I quickly find what triggered a 429?
A: Watch the browser network panel to see request counts per second and check server or application logs for spikes, noting the user, API key, IP address, and endpoint. Focus on hot endpoints such as login, search, or auth/token and compare the time window with provider limits to identify offending callers.
Q: What should I look for when an API returns 429 responses?
A: Read response headers like Retry-After, X-RateLimit-Limit, X-RateLimit-Remaining, and reset times, then pause requests until the reset time and resume at a lower rate. Also check your account dashboard for quota use and bursts, and consider upgrading or requesting higher limits if you regularly hit the cap.
Q: As a site owner, how should I configure rate limiting to reduce 429s?
A: Rate-limit by account or API key first and fall back to IP for anonymous users, using sliding windows or token buckets to allow short bursts while protecting the system. Return Retry-After with 429 to guide clients, cache heavy reads at CDNs or reverse proxies, and apply stricter limits and bot checks on hot endpoints like login or token routes.
Q: What retry strategy prevents causing or worsening a 429?
A: Always honor Retry-After and, if no header is provided, use exponential backoff with jitter (for example 1s, 2s, 4s, 8s plus a small random delay) while capping the number of retries. Avoid retrying unrelated errors such as 401, 403, or 5xx the same way, and log rate-limit events while surfacing clear messages to users.
Q: What long-term practices help prevent 429 errors from returning?
A: Space out and randomize background jobs, keep a safety margin under provider limits (for example target about 80% of max), and add dashboards for requests per second, error rates, and retry counts. Run load tests before big launches to validate backoff and queuing logic and educate your team so services do not retry simultaneously.