AI News
14 Apr 2026
Read 10 min
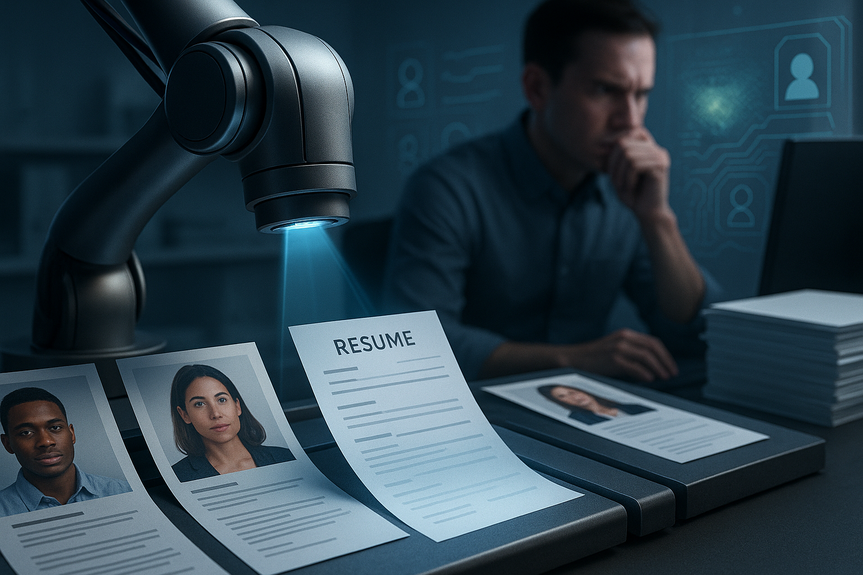
How to Defend Against Claude Mythos Cybersecurity Risks
Claude Mythos cybersecurity risks drove a Glasswing alliance that speeds patching to protect software.
What are Claude Mythos cybersecurity risks?
Mythos can scan code, spot subtle bugs, and suggest working exploits faster than most people. That means more zero-days may be found and weaponized quickly. The window from discovery to attack can shrink from months to minutes. The big risk is scale: an attacker with AI can hit many targets at once. Glasswing aims to give defenders a head start, but every team should act as if these tools are already in the wild. Addressing Claude Mythos cybersecurity risks starts with strong basics, backed by automation.Immediate steps to lower exposure
Know your assets and attack surface
- Keep a live inventory of internet-facing apps, APIs, devices, and cloud services.
- Map your software supply chain. Generate SBOMs for key apps and track risky dependencies.
- Scan for exposed ports, default creds, and shadow IT. Remove what you do not need.
Patch faster, shield when you cannot
- Prioritize fixes for internet-facing and high-value systems first.
- Use virtual patching: WAF rules, RASP, feature flags, and config changes to block known bug paths.
- Subscribe to vendor and CERT alerts. Watch for Glasswing-driven advisories and move quickly.
- Automate patch testing and rollout to cut time-to-fix from weeks to days or hours.
Harden code and builds
- Prefer memory-safe languages for new work (for example, Rust, Go). Reduce use of unsafe C/C++ in critical paths.
- Turn on compiler and platform guards: ASLR, DEP, stack canaries, CFI, sandboxing.
- Adopt secure coding checklists and pre-commit hooks. Enforce code review for security changes.
- Run SAST, DAST, and dependency scanning on every build. Fail builds on critical issues.
- Use fuzzing (including AI-guided fuzzing) to find edge-case bugs before release.
- Sign, verify, and make builds reproducible. Lock versions and verify hashes.
Control access and blast radius
- Enforce MFA everywhere, especially for admins, VPN, and code repos.
- Use least privilege. Rotate and vault secrets. Remove stale keys and accounts.
- Segment networks. Isolate prod from dev and test. Limit lateral movement.
- Adopt just-in-time access for sensitive actions and log every elevation.
Detect fast, respond faster
- Deploy EDR/XDR across endpoints and servers. Stream logs to a SIEM.
- Set alerts for new admin users, odd service changes, and unusual outbound traffic.
- Plant canary files, tokens, or honey endpoints to catch intruders early.
- Automate containment: isolate hosts, kill processes, block domains, and roll back changes.
- Test restores often. Aim for fast recovery times with clean, offline backups.
Prepare for AI-driven vulnerability discovery
Use AI for defense, with guardrails
- Let approved AI tools help triage alerts, write detections, and draft patches.
- Keep sensitive code and secrets out of public AI tools. Use private, logged instances.
- Validate AI output with scanners and tests before merging or deploying.
Run controlled “Mythos-like” testing
- Task internal red teams and vetted partners to hunt for zero-days in staging.
- Expand bug bounties. Reward reports that include clear proof and safe repro steps.
- Adopt a strong vulnerability disclosure policy and coordinate fixes before release.
Share and learn with the community
- Join ISAC/ISAO groups. Feed and read threat intel daily.
- Track outputs from Glasswing partners and major vendors. Apply mitigations quickly.
- Share sanitized indicators and lessons learned to raise the whole sector’s defense.
Governance, policy, and training
Set clear rules
- Create simple secure development standards. Include threat modeling for high-risk features.
- Define an AI use policy: approved tools, data handling rules, and review steps.
- Require security sign-off before major releases or infra changes.
Train for speed and clarity
- Run tabletop drills for a sudden zero-day discovered and mass-exploited by AI.
- Keep short playbooks: who decides, who patches, who communicates.
- Give devs, IT, and support hands-on practice with real logs and mock incidents.
Key metrics to watch
- Mean time to patch critical, internet-facing flaws.
- Percent of crown-jewel systems with MFA, EDR, and network isolation.
- SBOM coverage across apps and services.
- Time from alert to confirmed triage and containment.
- Backup restore success rate and time-to-recover.
Tooling checklist
- Asset inventory and external attack surface management.
- Vulnerability scanning with exploit intel and prioritization.
- WAF/RASP for virtual patching and runtime protection.
- EDR/XDR, SIEM, and SOAR for detection and automated response.
- Secrets manager and strong IAM with MFA and least privilege.
- SBOM generator and software composition analysis.
- Static and dynamic code scanners plus fuzzing.
- Container and IaC scanning with policy enforcement.
- Patch and configuration management with safe rollback.
(Source: https://www.theguardian.com/technology/2026/apr/08/anthropic-ai-cybersecurity-software)
For more news: Click Here
FAQ
Contents